4 Social Engineering Tricks Cybercriminals Use to Get Your Data
What is Social Engineering?
Even if you don’t know it, you’re being socially engineered—and it’s been happening your whole life! From family to friends, everyone you interact with, social engineering happens every hour of every day.
- I’m feeling a bit off (what does that even mean?), hon, can you get the dishes done?
- I’m gonna hold my breath until I get that doll!
- You’ve been chosen! $100 Costco Gift Reward!
Social engineering is about manipulating you into doing something—sharing confidential information, performing an action—you wouldn’t normally do. And cyber criminals have been using social engineering tricks on you to access computer systems, gather info, and even blackmail.
Milestone has put together a simple guide to help you protect yourself from social engineering attacks.
4 Tips on How to Say “Sayonara” to Cybercriminals
Find out what hackers are doing these days to trick you getting your info and how to tell them to vamoose:
1. See malicious links by hovering—not clicking—your mouse
One of the oldest tricks in the books, cybercriminals will send you a phishing email that looks legit. But buried not-so-deep are links that look OK to trick you into visiting an unsafe web page or downloading spyware/malware/ransomware that gives a cybercriminal access to your computer.
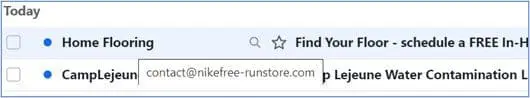
In fact, I just told my 80-year old mother to use this trick a few weeks ago. Before you click a link—image, email, text—hover your mouse over it. The address that pops up should match the email sender or web site you’re going to.
2. Copy the URL and paste it in the address bar to avoid dangerous web pages
Still want to click that link instead of just hovering? Or say, the link looks good (but has an unnoticed misspelling – amzon.com instead of amazon.com). Instead of clicking the link or button in an email to visit a web site:
- Right click the link
- Select Copy Link (or Copy Link Address)
- Paste the link in the address bar
Does the link look real? More often than not, if it’s a malicious site, a warning will appear before you actually get to the site. It’s the “not” you’ve got to be wary of.
3. Make sure the site is legitimate
Cybercriminals are tricky and play on our desire to be liked by the rich and famous. Malicious emails may impersonate a celebrity or someone you know to trick you into disclosing sensitive information by clicking an unsafe link or downloading a malicious attachment.
Cybercriminals will create fake web pages to trick you into signing into your account and get your username and password. Once you’ve entered your login credentials, cybercriminals can log in to your actual account, change your password, and get even more valuable info like your:
- Residential address
- DOB
- Credit cards
- SSN# (if it’s a credit card or healthcare site)
Fake pages are looking better and better these days, and will often mimic a real site down to a T. Since these fake web pages seem real, you may not even be aware you’re doing anything unsafe until it’s too late.
4. Keep in mind, if it seems suspicious, it’s suspicious
If someone you know messages you to ask about your organization or sends you a link, call or text the person directly to make sure the request is legitimate. If a message seems suspicious, it likely is suspicious.
Or even worse, you could receive a phone call from a cybercriminal pretending to be your phone company or other utility, or even a long-lost relative. If they have one piece of easy-to-find info (like an account number) and tell you your payment is late, you may be tempted to provide your credit or bank information.
Contact us for a free consultation.






